A “traditional” signature is used to verify many documents such as business deals, contracts, or bank cheques. But as we are moving into a more digitized world, the question will be: how can we verify the integrity of a digital document? The answer to this question is using digital signatures with blockchain.
In this post, we will be defining and explaining digital signatures, their uses, and how they work.
For our readers who are blockchain developers and want a more technical explanation, you can jump to this section where we showcase source code for creating digital signatures using a blockchain.
Table of contents
- How digital signatures work
- Advantages of digital signatures
- The role of digital signatures in blockchain
- Verify and seal your digital assets
What is a digital signature in blockchain?
A digital signature is a type of signature for documents that are stored digitally and that provides the highest level of assurance of a signer’s identity.
In fact, digital signatures are the next generation of document signatures – using online techniques that cut costs, are more environment-friendly, and require less time.
Digital signatures are the digital equivalent of regular ink signatures. In the same way, that legacy signatures are used to signal your approval on a paper and its contents, a digital signature is used to signal the same but on digital documents.
In other words, a digital signature consists of an electronic signature that is produced by one, and only one, possible signer. You can create digital signatures with many different apps – some of those are directed at signing PDFs and others provide data signing capabilities like dHealth Network’s Wallet.
List of apps to create digital signatures
Here are some apps that use blockchain technology and leverage the features of digital signatures.
- Zoho: Blockchain-based timestamping
- Leewayhertz: Blockchain document signing platform
- OpenSig: Open digital signature scheme that allows you to digitally sign electronic documents
- Sign.co: E-signature solution built on the blockchain technology
How digital signatures work
At the heart of this technology lays a Public Key Infrastructure (PKI) that foresees the use of a pair of keys, of which one end – the public key – is intended to be public and the other end – the private key – is held only by the signer in person.
Keys that are used for creating digital signatures consist of cryptographic keys, often represented in hexadecimal format. This enables high accuracy on acceptance of documents as well as provides higher security by reducing the chances for malicious actors to sign documents on your behalf.
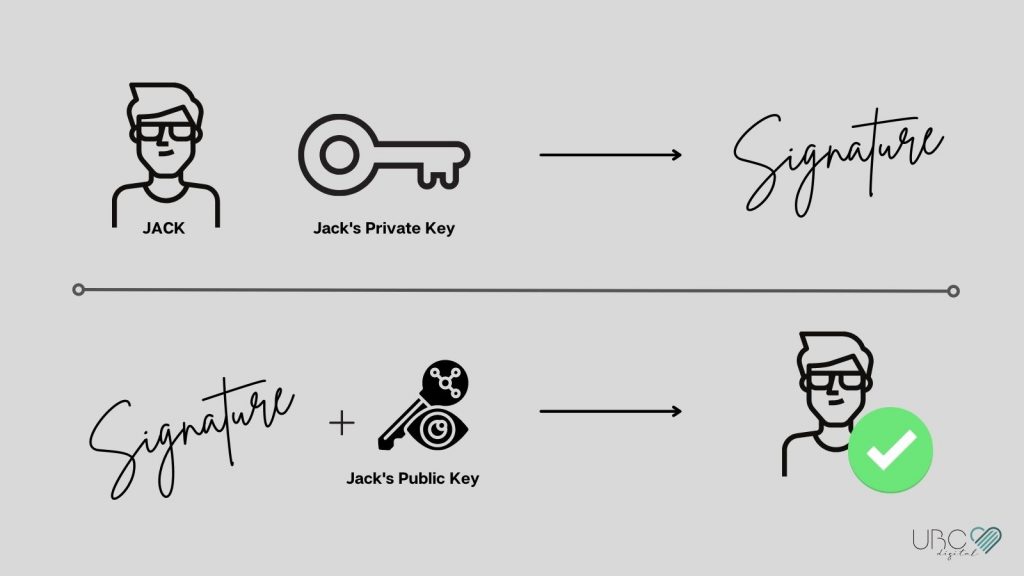
Take an example of Jack, who wants to sign a digital document and broadcast the result on a blockchain network. In order to do that, Jack will have to use a private key to sign the document using a predefined cryptographic algorithm to create digital signatures (e.g. ECDSA). The generated signature is unique to the combination of 1. Jack’s private key and 2. the document.
If anything changes from either of 1 or 2, it would create a completely different result – thereby ensuring integrity can be verified.
No one can change or forge Jack’s signature (because only Jack himself knows his private key).
Everyone who has knowledge of Jack’s public key is able to verify that the document is signed by Jack.
Advantages of digital signatures
Here are 4 main points that make digital signatures superior to traditional paper signatures and that makes them a necessity in our everyday life:
- Unforgeable: Digital signatures are unforgeable because it involves public-key cryptography. Just one byte- or character change creates a different output. Someone trying to create a digital signature must own the correct private key, thereby making it complicated for malicious actors to forge signatures.
- Secure: Given that it is much more complicated – if at all possible – to forge a digital signature, they present a secure alternative to signing documents compared to regular ink signatures on paper documents.
- Durable: Digital signatures are future-proof as it is always possible to verify a digital signature whereas a regular ink signature may fade off with time due to the ink or paper decomposition process.
- Ensures integrity: In the unlikely scenario that a digital signature was tampered with, the signature will become invalid and it will reveal that it has been edited.
Uses of digital signatures
Pascal got into trouble at school today and the teacher, Miss Elizabeth Hoover, has given him a paper document for his parent’s to sign before the next day. Pascal – with a malicious intent – decides to fake the signature of his parents. The next day at school, Miss Hoover has a hard time to determine whether this signature that she received is indeed from Pascal’s parents – in fact, Pascal could have forged it.
The above example illustrates how there is no possibility for the teacher, Miss Hoover, to verify the authenticity of the signature she received. A digital equivalent of the above would easily have triggered Miss Hoover’s alerts – forging is not possible here.
Digital signatures have the potential to unlock tremendous changes to our daily life- not only taking kids the ability to forge signatures- but rather, also, improving our human processes of signing legal documents, verifying government-issued documents, generally time-stamping data, or digitally signing e-mails that we send out daily.
In an attempt to showcase the use of digital signatures in combination with a blockchain network, I will sign a message with my dHealth Wallet which contains a message that reads:
Hello, from UBC Digital Magazine on Sept. 21 2021 – 21:21.
This message will be signed with my public account address NCXFYCJKVZYP3KSADNBI6624VH4BPFQICNIRFVY. This address can be shared publicly and identifies me following the above statement. Taking my dHealth Wallet, I added the message in a transaction and I signed it using my private key (which, obviously, I will not reveal).
The resulting transaction was broadcasted to the dHealth Network and you can see details about this transaction here.
“All those numbers”! Yes, digital signatures tend to be quite complicated to read for human eyes, at least at first sight. What is important with the above is that I used a private key to generate a signature. This signature could not have been created by someone else than by myself – only by the owner of said private key. And the most useful part is that the digital signature is verifiable. This means that it is possible to tell – also in 20 years – whether the signature was created with the private key corresponding to the account above, or whether it was created with a different account’s private key. Have you found out whether it’s the case? Tell us in the comments below.
Digital signatures are sometimes also leveraged to sign transactions on distributed ledger and/or verify ownership of digital assets. Now, let’s dive deeper into the creation of digital signatures on the blockchain and explain how we would implement a digital signature with some simple source code.
The role of digital signatures in blockchain
In the blockchain field, digital signatures must be created to authorize the transfer of assets and can be used otherwise to reflect the approval for other actions as illustrated below.
It is common for blockchain users to hold a private key that must be carefully secured. They can use this key with Wallet Software to sign transactions [digitally].
Signing transactions with private keys
To illustrate the creation of digital signatures for blockchain transactions, we will use the following action description: Alice owns 134.346723 DHP and wants to send 3 DHP to Bob.
In order to unlock the assets, Alice must create a transaction that holds an amount of DHP and a recipient public key. The recipient public key is the piece of data that identifies Bob in the transaction.
But before this transaction is accepted by a blockchain network, Alice must actually sign it with her private key, which only she knows about. When Alice signed the transaction, a digital signature can be shared with the blockchain network to execute the transaction.
Let’s see how the signature process would be implemented in a small snippet of source code using the well-known tweetnacl open source library.
// – Import dependencies
import * as nacl from ‘tweetnacl’;
// – Configure Alice’s account
const privateKey = ‘1CBA7612137ED84AAD4FB8D6EAC948D8AC079938973E2416FD10D6B2DCA63250’;
const publicKey = ‘213C1D2CD5C2180C3D55302278138AFDF0850ACC1E4F62567D56C12DFB987B44’;
// – (1) Create a “key pair”
const keyPair = new Uint8Array(64);
alicePrivate.set(privateKey);
alicePrivate.set(publicKey, 32);
// – (2) Prepare the transaction data, currently unsigned
const transaction = “send(3, ‘DHP’, ‘Bob’)”;
// – (3) Sign the transaction with Alice’s key pair
const signedTransaction = nacl.sign.detached(transaction, keyPair);
console.log(signedTransaction);
Verifying a digital signature
Regular ink signatures can be falsified or forged, which makes them insecure. On the other hand, with digital signatures on the blockchain, it is trivial to verify whether the signature is valid and also whether it was issued by whom claims to be the signer.
In fact, the verification process fits in a small snippet of source code. Taking the example of a verifier Carol, external to the transaction between Alice and Bob, she can easily verify the authenticity of the transaction by including Alice’s public key in her verification. That also counts for Bob, it is simple for Bob to verify that the provided digital signature was issued by Alice, by including her public key in the verification process.
Following example source code can be used to verify that Alice is indeed the signer of the above transaction, without knowing Alice’s private key.
// – Import dependencies
import * as nacl from ‘tweetnacl’;
// – (1) Configure Alice’s account
const alicePublicKey = ‘213C1D2CD5C2180C3D55302278138AFDF0850ACC1E4F62567D56C12DFB987B44’;
// – (2) Prepare the transaction data
const transaction = “send(3, ‘DHP’, ‘Bob’)”;
// – (3) Verify that Alice is the signer of “signedTransaction” bytes
console.log(“VERIFY: “, nacl.sign.detached.verify(
transaction,
signedTransaction,
alicePublicKey,
));
This same process is what goes on under the hood with blockchain networks and accounts that create transactions and broadcast signed copies of these to authorize asset transfers and other actions.
Verify and seal your digital assets
With digitalization taking a bigger place in our society, it also becomes more important to securely store your digital assets. Those can include your online books (e-books), the music you bought from a streaming platform, or any kind of tokens that are issued with blockchain networks.
Digital signatures can help in creating and verifying the integrity of your data. In fact, when Alice signed the data in the above example, just one byte- or character change would have created a completely different signature.
Verifying the integrity of data
Have your digital assets been tampered with-? Did someone run an exploit and modify your digital assets? Did you lose some of your digital assets?
These three questions can be answered astonishingly fast with digital signatures. In fact, because digital signatures often produce deterministic signatures – a combination of a private key and some data would always return the same digital signature.
In turn, this fact makes it easier to determine if data was modified (“tampered with”) and permits to adopt a different approach to discovering data breaches or fraudsters that share unlawful copies of your digital assets.
Sealing your digital assets
Additionally, you can create seals to protect access to your digital assets by adding secure, legal, and trusted electronic seals to them. These types of seals are useful to certify the integrity as well as to show the origin of your digital assets or documents.
For example, businesses may apply such seals on invoices before they send a contract to their customer. Through an electronic seal, the business ensures that the invoice won’t be modified in the future and the customer can rest assured that they know the terms of the transaction(s).

We hope that this article was insightful for you and are looking forward to any feedback and messages. Please share your thoughts in the comments section below!
Disclaimer
This website may contain information about financial firms, employees of such firms, and/or their products and services such as real estate, stocks, bonds, and other types of investments. While this website may intend - as the author deem necessary - to provide information on financial matters and investments, such information or references should not be construed or interpreted as investment advice or viewed as an endorsement.



Hi
I read your article and found it very helpful, thanks for sharing.